n00bzCTF 2024
Passwordless
给了源码
#!/usr/bin/env python3
from flask import Flask, request, redirect, render_template, render_template_string
import subprocess
import urllib
import uuid
global leetapp = Flask(__name__)
flag = open('/flag.txt').read()
leet=uuid.UUID('13371337-1337-1337-1337-133713371337')@app.route('/',methods=['GET','POST'])
def main():global usernameif request.method == 'GET':return render_template('index.html')elif request.method == 'POST':username = request.values['username']if username == 'admin123':return 'Stop trying to act like you are the admin!'uid = uuid.uuid5(leet,username) # super secure!return redirect(f'/{uid}')@app.route('/<uid>')
def user_page(uid):if uid != str(uuid.uuid5(leet,'admin123')):return f'Welcome! No flag for you :('else:return flagif __name__ == '__main__':app.run(host='0.0.0.0', port=1337)
uuid和username
获取uid 得到url
访问得到flag
LIT CTF
anti-inspect
没看提示 打开链接了崩了.. 还纳闷咋打不开..
向题目链接发出请求

jwt-1
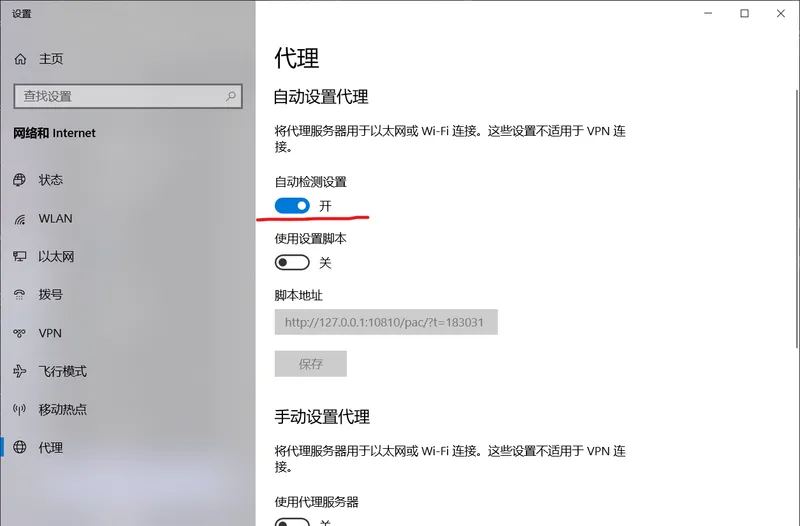
读提示和token有关 在加上jwt
获取token


将false改成true 保存token


jwt-2

老方法先试一下

发现是上一道题的flag
查看源码

伪造令牌 绕过检查



traversed

![[c++][笔记]浅谈几种排序方式---冒泡排序,选择排序,桶排序](https://i-blog.csdnimg.cn/blog_migrate/bc8a9912f213fb0724dd4bd4db3a4331.gif)