【实验目的】实现两台linux主机可以通过SSH实现异地互连。
【实验条件】两台linux虚拟机
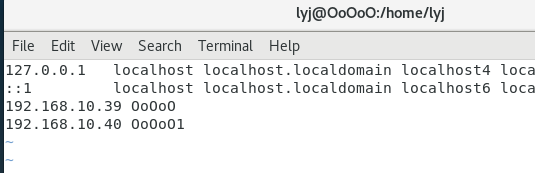
OoOoO:192.168.10.39
OoOoO1:192.168.10.40
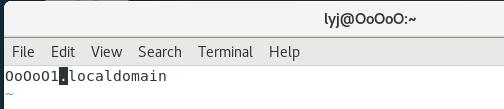
改主机名:
[root@localhost ~]# vim /etc/hostname
在hosts文件中做映射:
[root@localhost ~] #vim /etc/hosts
[root@localhost ~]# reboot
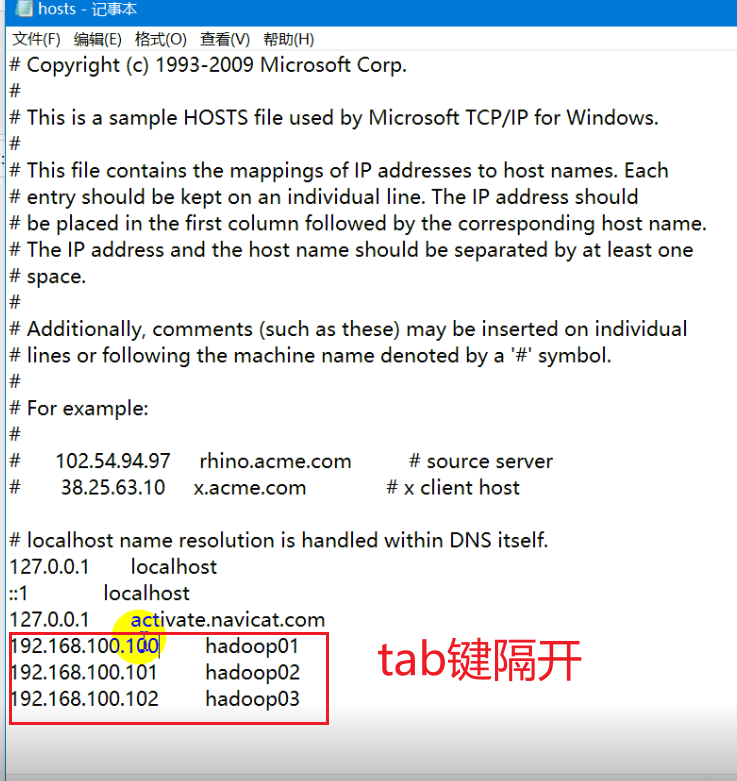
查看有没有安装ssh服务:
[root@OoOoO lyj]# rpm -qa|grep ssh
openssh-7.4p1-21.el7.x86_64
openssh-clients-7.4p1-21.el7.x86_64
openssh-server-7.4p1-21.el7.x86_64
libssh2-1.8.0-4.el7.x86_64
查看ssh服务有没有运行:
[root@OoOoO lyj]# ps -e | grep sshd
1163 ? 00:00:00 sshd
如果有显示出结果,就说明有运行。
首先,在一台上面产生公钥私钥。
【OoOoO】配置,如下:
[root@OoOoO lyj]# pwd
/home/lyj
[root@OoOoO lyj]# ssh
ssh ssh-agent sshd ssh-keygen
ssh-add ssh-copy-id sshd-keygen ssh-keyscan
[root@OoOoO lyj]# ssh-keygen
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa):
Created directory '/root/.ssh'.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_rsa.
Your public key has been saved in /root/.ssh/id_rsa.pub.
The key fingerprint is:
SHA256:LQsynPxjm6yuaIUa8YrA1SPgWBgQC5Xn1PMU+AFJSNs root@OoOoO.localdomain
The key's randomart image is:
+---[RSA 2048]----+
|*=.o.+o+.. |
|ooo +o= o |
|+..+o E= . |
|o. =.+ o. |
|.oo B o S . |
|oo.. + . o |
|+o. + . |
|+o o + |
|o .oo.+ |
+----[SHA256]-----+
[root@OoOoO lyj]# cd /root/.ssh
[root@OoOoO .ssh]# ls
id_rsa
id_rsa.pub
公钥扩展名:.pud
一对公钥,一对私钥。
【OoOoO1】配置,如下:
[root@OoOoO1 lyj]# ssh
ssh ssh-agent sshd ssh-keygen
ssh-add ssh-copy-id sshd-keygen ssh-keyscan
[root@OoOoO1 lyj]# ssh-key
ssh-keygen ssh-keyscan
[root@OoOoO1 lyj]# ssh-keygen
Generating public/private rsa key pair.
Enter file in which to save the key (/root/.ssh/id_rsa):
Created directory '/root/.ssh'.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_rsa.
Your public key has been saved in /root/.ssh/id_rsa.pub.
The key fingerprint is:
SHA256:JRKmcel8nHGthkDirszTsim02Joia0X1DXdmJdhLF/Q root@OoOoO1.localdomain
The key's randomart image is:
+---[RSA 2048]----+
| o.=. ooo+. |
| . Boo.o.o.. |
| +ooo==.o E |
| o oo=+o. |
| . . .S. |
| + + |
|o.O . |
|=+.= |
|B+o |
+----[SHA256]-----+
[root@OoOoO1 lyj]#
现在要公钥私钥交换,把这2份(或者更多份)公钥私钥合并为同一份文件。
❗❗❗原理要懂
【OoOoO1】配置,如下:
[root@OoOoO1 lyj]# ssh-copy-id OoOoO
/usr/bin/ssh-copy-id: INFO: Source of key(s) to be installed: "/root/.ssh/id_rsa.pub"
The authenticity of host 'ooooo (192.168.10.39)' can't be established.
ECDSA key fingerprint is SHA256:lZmpTdhrMt7d6BML/ZQZZPXJXDQDVXPrxIB+R5KEHQ8.
ECDSA key fingerprint is MD5:f3:f1:e8:bd:f3:4c:25:85:6b:7a:cf:72:17:ac:46:bc.
Are you sure you want to continue connecting (yes/no)? yes
/usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
现在还没有免密,所以还需要yes
【OoOoO】配置,如下:
[root@OoOoO .ssh]# ssh-copy-id OoOoO
/usr/bin/ssh-copy-id: INFO: Source of key(s) to be installed: "/root/.ssh/id_rsa.pub"
The authenticity of host 'ooooo (192.168.10.39)' can't be established.
ECDSA key fingerprint is SHA256:lZmpTdhrMt7d6BML/ZQZZPXJXDQDVXPrxIB+R5KEHQ8.
ECDSA key fingerprint is MD5:f3:f1:e8:bd:f3:4c:25:85:6b:7a:cf:72:17:ac:46:bc.
Are you sure you want to continue connecting (yes/no)? yes
/usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
root@ooooo's password:
[root@OoOoO .ssh]# ls
authorized_keys
id_rsa
id_rsa.pub
known_hosts
[root@OoOoO .ssh]# pwd
/root/.ssh
多了一个文件 authorized_keys 包含这三台的公钥。
[root@OoOoO .ssh]# scp /root/.ssh/authorized_keys OoOoO1:/root/.ssh
The authenticity of host 'ooooo1 (192.168.10.40)' can't be established.
ECDSA key fingerprint is SHA256:lZmpTdhrMt7d6BML/ZQZZPXJXDQDVXPrxIB+R5KEHQ8.
ECDSA key fingerprint is MD5:f3:f1:e8:bd:f3:4c:25:85:6b:7a:cf:72:17:ac:46:bc.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added 'ooooo1,192.168.10.40' (ECDSA) to the list of known hosts.
root@ooooo1's password:
authorized_keys 100% 809 1.2MB/s 00:00
远程拷贝。
[root@OoOoO1 lyj]# cd /root/.ssh
[root@OoOoO1 .ssh]# ls
authorized_keys id_rsa id_rsa.pub known_hosts
[root@OoOoO1 .ssh]# source /etc/profile
记得source
测试是否免密生效。
[root@OoOoO .ssh]# ssh OoOoO1
Last login: Sun Jun 23 22:09:18 2024
[root@OoOoO1 ~]#
[root@OoOoO1 .ssh]# ssh OoOoO
Last failed login: Sun Jun 23 22:44:24 CST 2024 from ooooo1 on ssh:notty
There was 1 failed login attempt since the last successful login.
Last login: Sun Jun 23 22:05:48 2024
[root@OoOoO ~]#
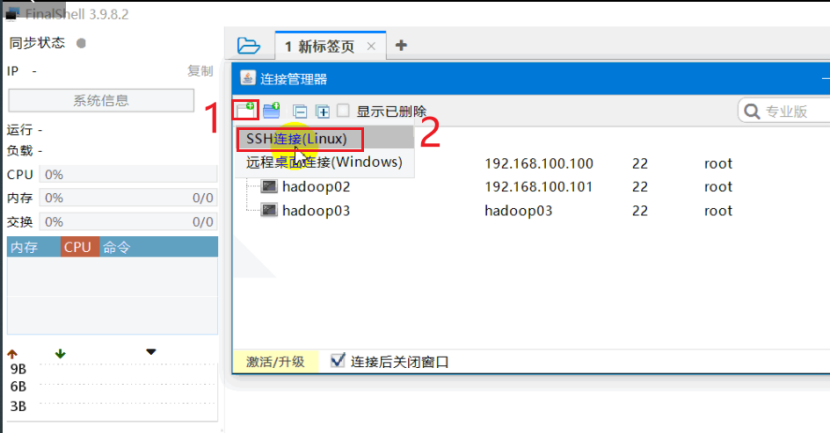
这里的主机名不能用hadoop01
需要先在物理机里面做映射。
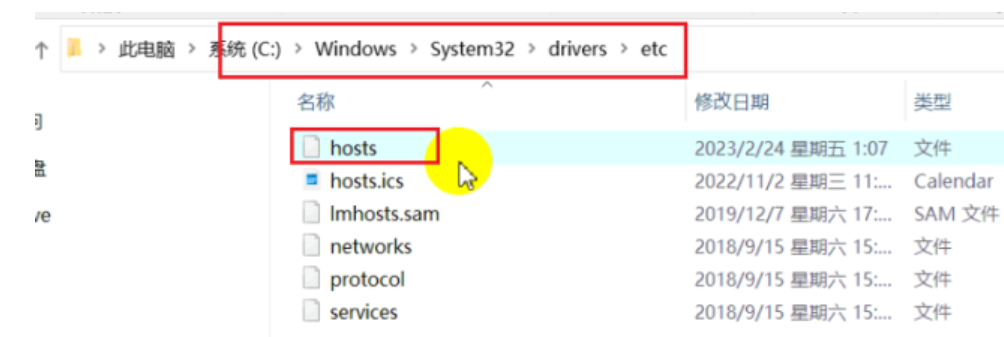
这个时候就可以用主机名访问。
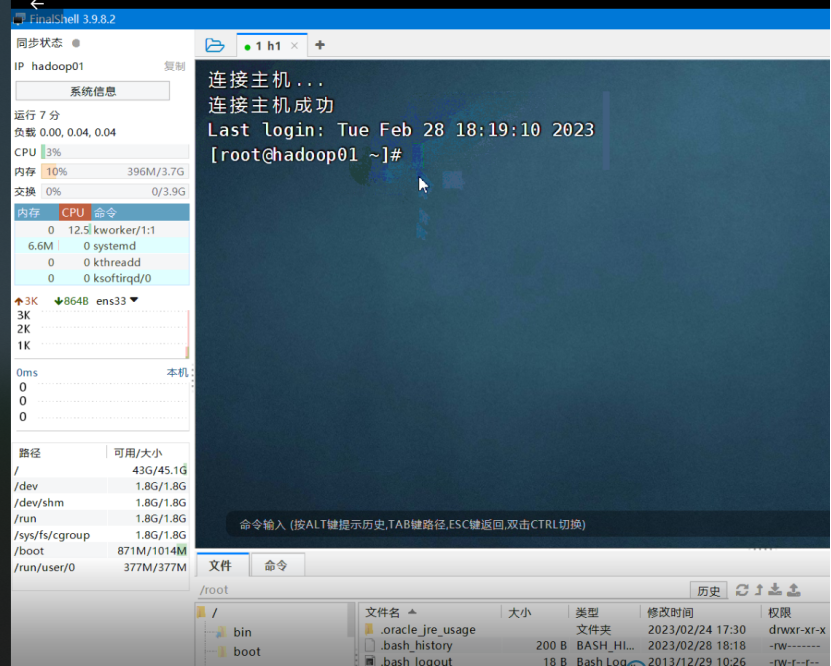
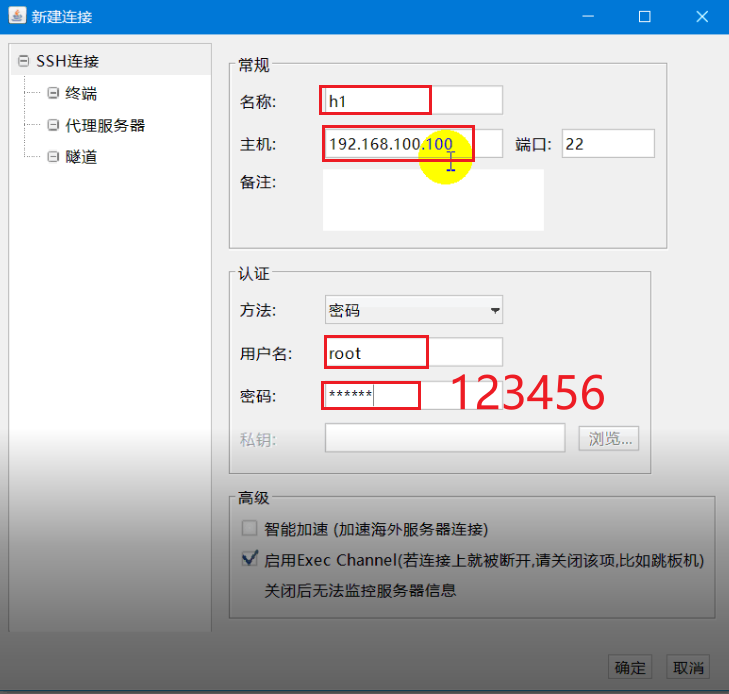
注意,开始演示登录的时候,使用的是root角色。
现在演示的是普通权限:
取决于用户名+密码。这涉及到后续的具体的操作任务。比如需要把物理机的文件传到linux里面,需要用到root权限。